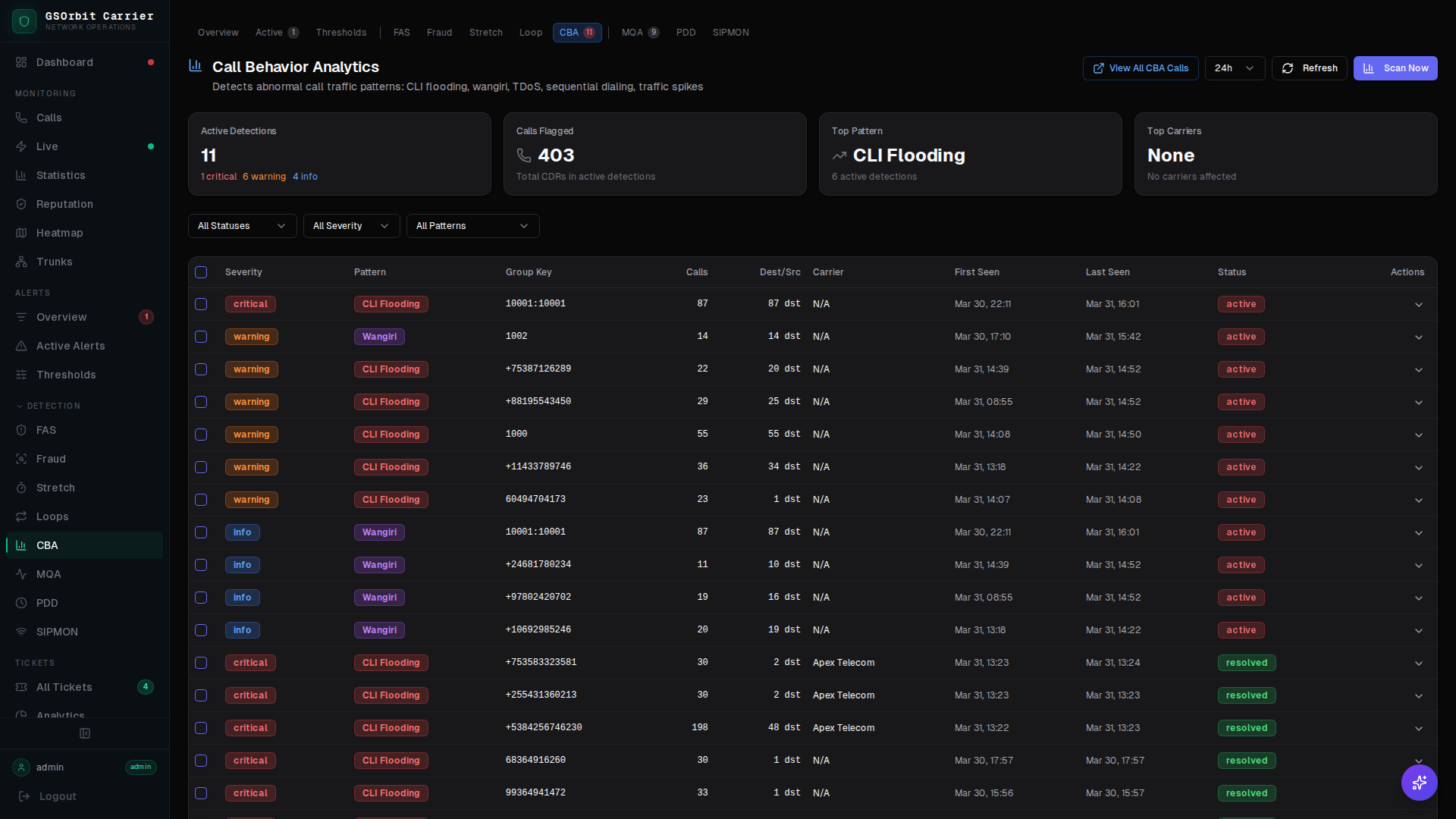
Call Behavior Analytics (CBA)
Behavioral fraud and abuse attacks have distinct calling patterns. CBA runs five specialized detectors simultaneously — each tuned for a specific attack type — so no pattern escapes detection.
The Call Behavior Abuse Problem
Behavioral attacks on VoIP infrastructure range from CLI flooding that overwhelms destinations to wangiri scams that trick customers into calling premium numbers. Each attack has a distinct signature that generic alerting misses.
- CLI flooding overwhelming destination numbers and triggering PSTN protection mechanisms that block legitimate calls
- Wangiri callbacks generating premium-rate charges for your customers from a single missed call
- TDoS attacks tying up your SIP infrastructure with high-volume fake call attempts
- Sequential dialing patterns indicating automated number harvesting or robocall campaigns originating from your network
- Unexpected traffic spikes causing capacity strain before your team has time to investigate
How CBA Detection Works
Five parallel detectors each run against live call stream data, each tuned for one attack class.
Detects when a single or small group of calling line identities generates call volume far above baseline — indicative of flooding or spoofed CLI campaigns.
Identifies single-ring-then-disconnect patterns from numbers in premium-rate destinations, flagging wangiri bait calls before customers call back.
Detects Telephony Denial of Service patterns — high-volume, short-duration call floods designed to exhaust SIP resources rather than complete calls.
Identifies calls to numerically sequential destination numbers — a signature of automated dialers performing number harvesting or robocall blasting.
Baseline-aware spike detection that distinguishes genuine demand increases from sudden abnormal volume that warrants investigation.
Why GSNOC CBA Is Different
- Five specialized detectors — each purpose-built for one attack type — rather than one generic anomaly detector trying to catch everything
- Baseline-aware detection means traffic spikes during known peak periods don't fire false alerts
- Cross-engine correlation surfaces CBA flags alongside fraud scanner and quality data for full call context
Key Metrics
Call volume per calling line identity relative to baseline — elevated values indicate flooding or spoofing
Which CBA detector fired: CLI flood, wangiri, TDoS, sequential dial, or traffic spike
Destination numbers targeted by the detected behavior pattern
Percentage increase in call volume above baseline at time of spike detection